Description: The County presents the opportunity to rotate through the different IT groups of the IT department. This blog will compare my time in Enterprise and will discuss what I learned.
Introduction
During the month of February, I had the opportunity as a cooperative education student to rotate through the Enterprise team. Enterprise is split between cybersecurity and computer/user management, and during my time there, I learned was mentored by one of my cybersecurity coworkers. Like how Help Desk covers the surface level issues of the Networking and Telephony team, Help Desk employees also tend to see surface level issues dealing with cyber as well, but as I was with the Enterprise team, I got to hear and see a lot more of the technical side of what the County does to ensure that all the private information and PII (personal identifiable information) that is handled is protected. So, now that I have experienced both the Helpdesk group and the Enterprise group, I want to compare the two and demonstrate what I have learned.
Palo Alto
Palo Alto is the leading cybersecurity company that offers a wide variety of protective services. Their single-pass parallel processing (SP3) hardware and their use of command line interface (CLI), which is typically accessed using a secure protocol like Secure Shell (SSH), make their firewall top-notch. The County uses Palo Alto’s firewall to protect all the internal private information and stop any potential external attacks from hackers. Palo Alto plays a crucial role in the County’s protection, and even though the use of their firewalls and applications can be complicated and expensive, it is worth using and the company is a great help in keeping all information secure.
Panorama
Panorama is an application from Palo Alto that allows the cybersecurity group to edit, delete, or add rules to the firewall. Each rule made and set does something different, like how a rule might not let users access a sketchy website because it does not meet the right requirements or how a rule might allow specific users to log into a specific application that has been blocked for everyone else. There were hundreds of rules written in Panorama, and some of them seemed so complicated that I could not quite understand what they did, but being able to look at the backend of what protects malicious data from reaching the County’s private information was very interesting, albeit a bit intimidating. Thankfully, due to being given specific previewing permissions, I did not have to worry about accidentally breaking something.
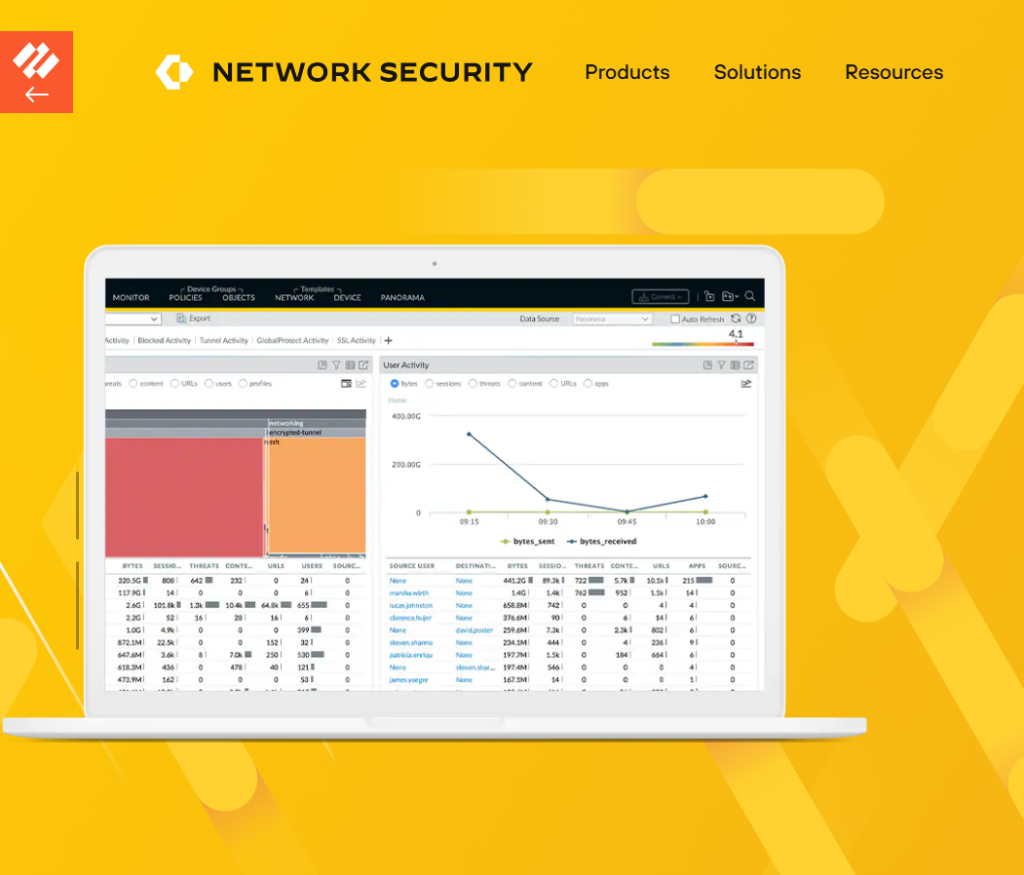
Panorama also allows for admins to go in and check the logs of requests going through the firewall. While I was looking through, I could see when I had signed in that morning, what I have accessed since then, and any requests my computer made to access a website. The log tracks the user’s name, what they attempted to access, and at what time, so if someone would demonstrate any malicious activity or malicious malware made its way to the firewall, the cyber team can trace where exactly the malicious intent was coming form.
Firewall
The County has two physical firewalls that are kept in a secure location. Only one of the firewalls are on at a time but should the one firewall turn off or become damaged, the second firewall has all the same rules copied into it, so that the cyber team can easily switch over to that firewall. This is a part of the physical security that the cyber team has to implement to ensure that, no matter what may happen, none of the data the firewall protects will ever be unprotected, even for a short period of time.
Phishing Tickets
With so many different departments within the County, as a way to keep employees vigilant, a phishing test is sent out each quarter to try and trick people into clocking the link. This is done so that the County can see how many employees are susceptible to a scam email and, if a user fails a phishing test twice, they are required to take a cybersecurity class so that they can be more cyber safe. Last quarter, we had an amazing score, ninety-nine percent of the County passed the test, including myself. We strive to keep increasing our numbers so that all our employees can remain safe, but if they do find an email that they are unsure if it is safe or a scam, they can always send it to IT for us to run.

Similarities/Differences
When it comes to the cybersecurity team, there are not as many places where Help Desk cross over as there were between Help Desk and the Networking/Telephony team. For the most part, Help Desk deals with most of the phishing tickets users send in. There is a specific button within every County employee’s Outlook account that says to “report the email as phishing,” and when a user clicks it, a ticket is created for us to run through our malware scanner. If the email is benign, then we message the user back saying the email is safe, if it is malicious, we email the user to not press anything and we send the ticket off to the cyber group. They will then purge the email from all email accounts so that no user can accidentally click the malicious email. I, myself, have already had a few scam emails be sent to users that needed to be purged, one of them having been sent to nearly thirty different employees.
Conclusion
In conclusion, at the end of the day, both the Enterprise group and Help Desk are essential in keeping the County’s IT systems running smoothly and County users cyber safe. The Help Desk remains the frontline, assisting users with everyday tech issues and ensuring they can do their jobs without disruption. Meanwhile, cybersecurity works behind the scenes to defend against threats, safeguard public data, and ensure compliance with regulations they put into place. Though there is not much crossover between the two groups, the groups go hand in hand-a strong firewall and Enterprise team prevent many issues from reaching the Help Desk, and a communicative Help Desk team helps enforce security policies.
